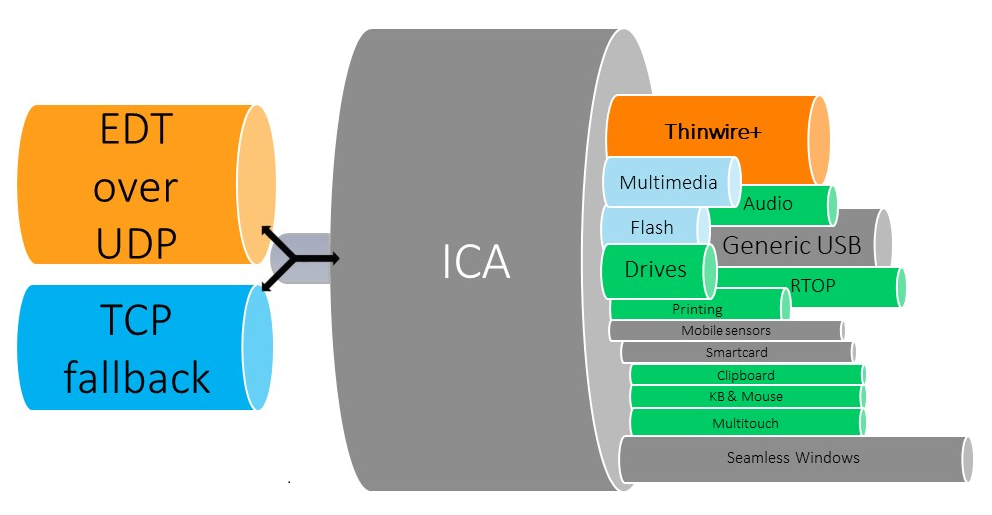
Adaptive transport is a data transport mechanism for Citrix Virtual Apps and Desktops. It is faster, can scale, improves application interactivity, and is more interactive on challenging long-haul WAN and internet connections. Adaptive transport maintains high server scalability and efficient use of bandwidth. By using adaptive transport, ICA virtual channels automatically respond to changing network conditions. They intelligently switch the underlying protocol between the Citrix protocol called Enlightened Data Transport (EDT) and TCP to deliver the best performance. It improves data throughput for all ICA virtual channels including Thinwire display remoting, file transfer (Client Drive Mapping), printing, and multimedia redirection. The same setting is applicable for both LAN and WAN conditions.
When set to Preferred, data transport over EDT is used as primary and fallback to TCP. With the Citirx Workspace app for Windows minimum version 1808 or Citrix Receiver for Windows minimum version 4.10 and session reliability enabled, EDT and TCP are attempted in parallel during the initial connection, session reliability reconnection, and auto client reconnect. Doing so reduces connection time if EDT is Preferred, but the required underlying UDP transport is unavailable and TCP must be used. By default, after fallback to TCP, adaptive transport continues to seek EDT every five minutes.
As you can see EDT is particularly useful for WAN connections to your Citrix Virtual Apps and Desktops. Those connections usually are established through a Citrix Gateway (Citrix ADC, known as Citrix NetScaler). EDT is supported on versions 11.1 build 51.21, 12.0 build 35.6 and later of Citrix Gateway (Citrix ADC). Unfortunately there is a bug in all builds newer than 13.0 36.27 which causes EDT connections to fail and always fallback to TCP.
Up to the recently discovered vulnerability in Citrix Application Delivery Controller and Citrix Gateway (CVE-2019-19781) this wasn’t too much of an issue, because you could stay on the working build and wait for an upcoming new release to fix the issue. Things changed dramatically with the vulnerability and the fixed builds Citrix released last month – it’s definitely NO option anymore to stay on one of the older builds and expose your Gatway / ADC to those security risks.
The issue with non working EDT over Citrix Gateway and Citrix ADC releases newer than build 13.0.36.27 is caused by a bug, which prevents DTLS from enabling. For the moment there is no other way than enabling DTLS manually over CLI by executing the following commands:
-
shell nsapimgr -ys enable_dtls12_vpn_vserver=1
-
set vpn vserver [vservername] dtls OFF
-
set vpn vserver [vservername] dtls ON
Make sure to run the first command in shell, while turning off and on of DTLS has to be executed in the CLI mode.
Keep in mind this workaround doesn’t survive a reboot and doesn’t persist. After a reboot DTLS stops working until you apply the workaround again. To persist the DTLS setting it should be possible to apply the workaround to rc.netscaler:
shell “echo ‘nsapimgr -ys enable_dtls12_vpn_vserver=1’ >> /nsconfig/rc.netscaler”
With this simple workaround your WAN connections will start working again over EDT, while you can keep your Citrix Gateways and Citrix ADCs on the latest fixed 13.0 build until one of the upcoming releases will permanently fix the underlying issue.